 There’s a saying in the tech support world: “the only 100% secure computer is the one encased in concrete and connected to nothing”. When you set up your home network, the challenge is to find a balance your computer security needs with functionality. To minimize risk without compromising your ability to enjoy your home network. Though no computer network can be risk-free, focusing on a few key issues can keep you up and running.
There’s a saying in the tech support world: “the only 100% secure computer is the one encased in concrete and connected to nothing”. When you set up your home network, the challenge is to find a balance your computer security needs with functionality. To minimize risk without compromising your ability to enjoy your home network. Though no computer network can be risk-free, focusing on a few key issues can keep you up and running.
Internet Security: The Technical Element
The first line of defence is the one that most people never think about: Wi-Fi. Too many people simply plug their wireless router in and walk away, leaving it vulnerable to intrusion. By spending just a few minutes correcting the default settings of the router, you can dramatically increase your network security. The default administrator username and password for these devices are widely known, and they should be the first configuration you change. Your router will also be set to broadcast the name of the network to any scanning device. By turning the broadcast off, anyone wanting to connect to your network will need to know its SSID name beforehand. Finally, a good password and strong encryption will make it very difficult for anyone to force their way onto your network. The current standard for wireless encryption is WPA2, and as long as it is compatible with all of your wireless devices, it’s the one to go with.
 The next necessity for your home network’s cyber security is a firewall.
The next necessity for your home network’s cyber security is a firewall.
A firewall restricts access to your network from the internet. With thousands of automated virus-infected computers constantly scanning for open and exploitable computers, you need to close the doors they are looking to sneak through. Your firewall can be a software solution running on your computer itself, like the Windows Firewall program that’s built in to Windows 8. Or, the firewall can be a part of your network router.
The D-Link Dual Band Router is an example of a network router that includes a firewall. The advantage of a router-based firewall is simple management for your entire network. If you rely on the software contained on each individual computer, you run the risk of accidentally leaving one computer exposed. And the centralized firewall will also protect visiting devices using your network.
Virus protection is your next level of defence. The default Windows Defender program is capable enough, as are the free versions of the most popular anti-virus software, but there’s better coverage to be found with the paid versions.
A paid anti-virus program will cover multiple devices in your home and provide updates at a speed that the free versions just can’t match.
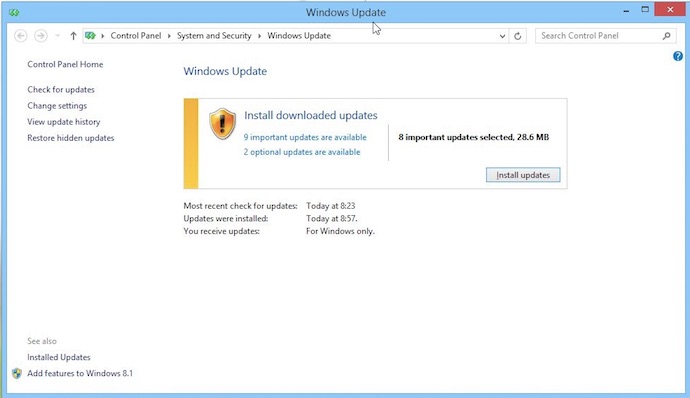
Speaking of updates, your operating system needs attention.
Operating system developers are in a continual game of cat and mouse with the hackers looking for the next vulnerability to exploit. By setting your OS to update automatically, you’ll have the most recent fixes to the existing weaknesses. These updates can come weekly, or even every few days, and managing them manually is an unnecessary inconvenience. Keep in mind, however, that occasionally there are compatibility issues between new updates and older software running on your computer. If you have a program that you cannot live without in the short term, manual system updates give you the control over the timing of installation.
And even with the best proactive configuration, something unwanted can slip through your defences and affect your computer.
Regularly scheduled virus scans are a must. It’s also a good idea to add anti-malware and anti-adware scanning to your maintenance routine. Malware is a category of malicious software that isn’t strictly speaking a virus, so your anti-virus doesn’t catch it. Malware attempts to take information from your computer, or manipulate your computer so that an unknown third party can gain access and control. Some malware is designed to track your internet browsing habits and report them back to a central tracking system. Usually the tracking is complemented by another type of unrequested intrusive software called adware. These programs display ads for various products within your browser, and attempt to control your search results to send you to their preferred sales site instead of where you actually wanted to go.

Internet Security: The Human Element
With the technological side of the secure network equation taken care of, it’s time to focus on the more complicated component: you, the user.
There’s no amount of installed software that can keep you safe from unwelcome online activity if you put yourself in exposed situations. The threat comes in the form of social engineering, the practice of using psychological manipulation to trick the unwary user into divulging personal information. By creating elaborate and believable situations, the manipulator lulls you into trusting them and revealing usernames, passwords, and financial details. One of the most common social engineering tactics is called “phishing.” A phishing site appears to be from a legitimate company, but it is in fact a counterfeit website that will collect whatever information you enter and sell it to the highest bidder. Remember that no reputable company will request personal log-in information via email. Make sure to check the web address in your browser bar whenever financial information is concerned. A secure website will have an icon of a lock in front of the web address, which means that any information transmitted is safely encrypted. Spelling mistakes and misleading web links are also red flags, warning you that the site you’re on shouldn’t be trusted.
 And, internet safety means more than just protecting your data. It also means protecting yourself from harmful online interactions. An online community can be a great source of information and virtual support. It can also become a toxic and harmful environment very quickly. As much as we want to believe that we can pre-emptively avoid the pitfalls of harmful online interaction, the truth is that everyone is susceptible to toxic online situations, like being the target of cyber bullying. Protecting your privacy by controlling what personal details you share on social media is incredibly important. Every fact that you share with the online world at large will be accessible to someone looking to attack you. If you do find yourself targeted by a hostile and abusive person, resist the urge to respond to them. Your angry response is what they’re looking for, and it will only trigger more abuse. Instead, inform the moderators or administrators of the site that the abusive behaviour is taking place.
And, internet safety means more than just protecting your data. It also means protecting yourself from harmful online interactions. An online community can be a great source of information and virtual support. It can also become a toxic and harmful environment very quickly. As much as we want to believe that we can pre-emptively avoid the pitfalls of harmful online interaction, the truth is that everyone is susceptible to toxic online situations, like being the target of cyber bullying. Protecting your privacy by controlling what personal details you share on social media is incredibly important. Every fact that you share with the online world at large will be accessible to someone looking to attack you. If you do find yourself targeted by a hostile and abusive person, resist the urge to respond to them. Your angry response is what they’re looking for, and it will only trigger more abuse. Instead, inform the moderators or administrators of the site that the abusive behaviour is taking place.
Images from D-link.com, Linksys.com and Digicert.com



